Welcome to the first installment of Ironcore’s Zero Trust educational series; Zero Trust – Data!
In its most basic form, cyber security is designed to prevent unauthorized access to your institution’s data. But while that sounds simple, protecting your data has become very complicated. There are many methods that bad actors utilize in attempt to gain access to your data, including social engineering, taking advantage of flawed or vulnerable applications and operating systems, malware, and sneaking past your firewalls and into your network via the internet. Because there are huge amounts of money involved, the bad actors are very motivated to do whatever it takes to be successful in their attempts to get past your defenses and access your sensitive data.
Along with this motivation comes creativity, as bad guys continue to create new and imaginative methods to get past your defenses. Zero Trust cyber security is a fundamental change in the way cyber security defenses operate when compared to the cyber defenses that have traditionally been utilized in the past.
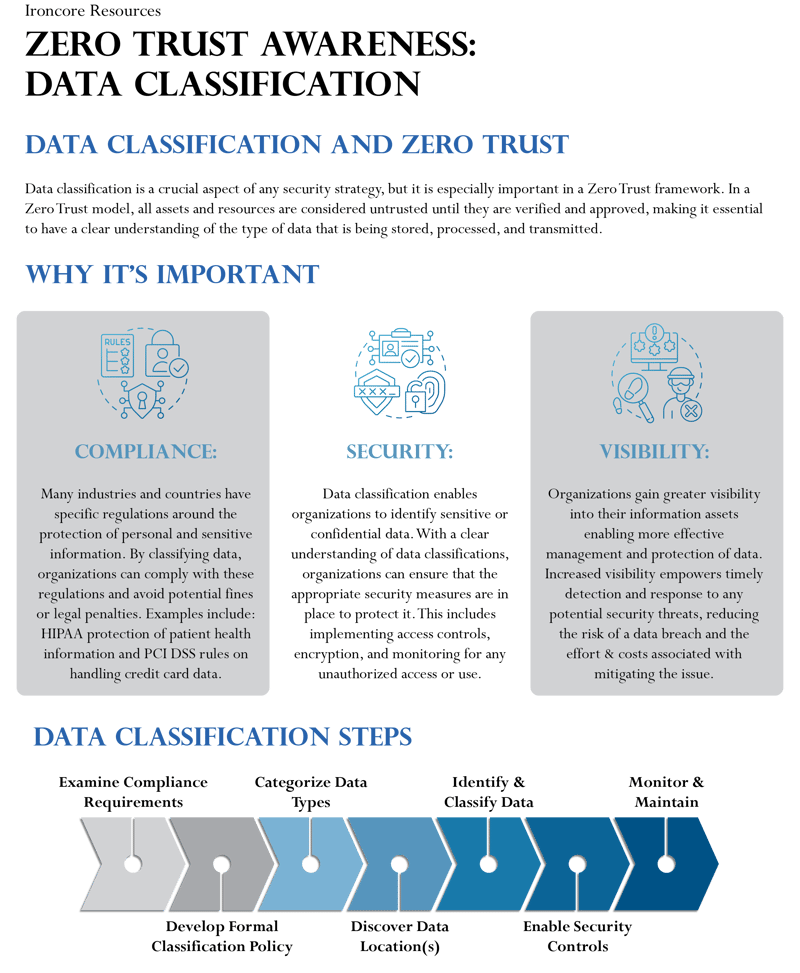
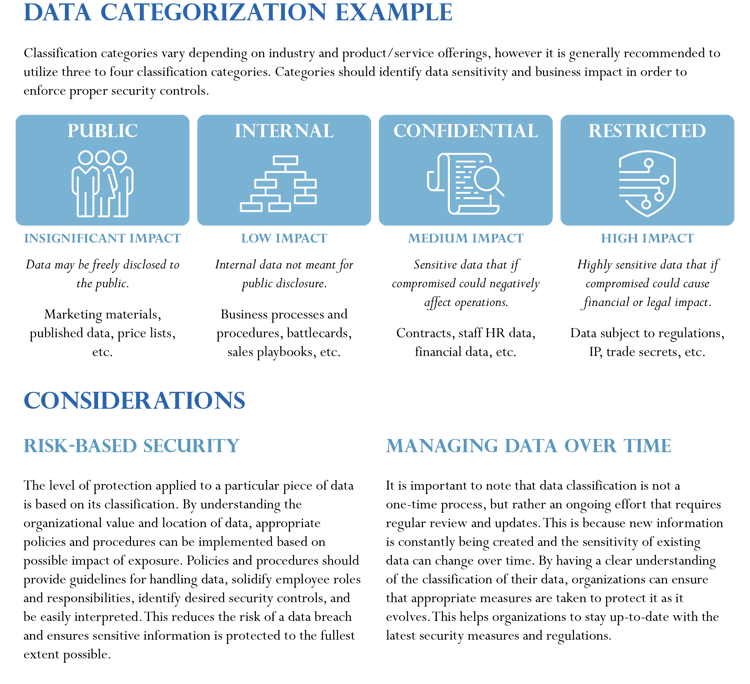
A Zero Trust framework is designed as layers working in concert, each one specifically engineered to prevent unauthorized access within different parts of your network. Zero Trust policies and services provide layers of protections for six different areas; Data, Identities (Users), End Points, Applications, Network, and Infrastructure. As your data is the ultimate target, this first session outlines why Zero Trust Data Classification is a crucial aspect of your security strategy.
Click here for a printable version of this flyer.
 Our Zero Trust series is available to you and anyone else in your organization. We encourage you to share this information with anyone inside or outside of your organization that may benefit from this series.
Our Zero Trust series is available to you and anyone else in your organization. We encourage you to share this information with anyone inside or outside of your organization that may benefit from this series.
If you have any questions about what you see here, please feel free to contact us at zerotrust@ironcore-inc.com. We will be happy to provide additional information.